The term "lauren kimripley leak" refers to a specific incident involving the unauthorized release of private or sensitive information belonging to an individual named Lauren Kimripley. Such leaks can encompass a wide range of personal data, including private communications, financial records, or other confidential details.
Leaks of this nature can have severe consequences for the affected individual, potentially causing reputational damage, financial loss, or even threats to personal safety. It is crucial to emphasize the importance of protecting one's privacy and taking measures to safeguard sensitive information from unauthorized access or disclosure.
Understanding the potential risks associated with data leaks can empower individuals to take proactive steps to protect their personal information. By being aware of the various methods used to obtain and distribute sensitive data, individuals can make informed decisions about their online behavior and interactions.
lauren kimripley leak
The "lauren kimripley leak" highlights the critical importance of safeguarding personal information and data privacy. Key aspects to consider include:
- Unauthorized Access: Gaining access to private data without permission.
- Data Breach: A security incident leading to unauthorized access to sensitive information.
- Identity Theft: Using stolen personal information to commit fraud or other crimes.
- Reputational Damage: Negative impact on an individual's reputation due to leaked information.
- Financial Loss: Monetary damages resulting from unauthorized access to financial data.
- Privacy Violation: Infringement on an individual's right to keep their personal information confidential.
- Legal Consequences: Potential legal penalties for those responsible for data leaks.
- Cybersecurity Measures: Steps taken to protect against unauthorized access to data.
Understanding these aspects empowers individuals to take proactive measures to safeguard their personal information, such as using strong passwords, being cautious about sharing sensitive data online, and being aware of the potential risks associated with data breaches. Additionally, organizations must prioritize robust cybersecurity measures to prevent unauthorized access and protect the privacy of their customers and employees.
Unauthorized Access
Unauthorized access to private data, a critical component of the "lauren kimripley leak," occurs when individuals obtain access to sensitive information without authorization. This can happen through various methods, such as hacking, phishing, or exploiting software vulnerabilities. Unauthorized access can have devastating consequences, leading to identity theft, financial loss, and reputational damage.
In the case of the "lauren kimripley leak," unauthorized access was gained through a data breach. Hackers exploited a vulnerability in a software system to gain access to a database containing personal information, including names, addresses, and financial data. This breach highlights the importance of strong cybersecurity measures to prevent unauthorized access and protect sensitive information.
Understanding the connection between unauthorized access and data leaks empowers individuals and organizations to take proactive steps to safeguard their data. By implementing robust cybersecurity measures, using strong passwords, and being cautious about sharing personal information online, individuals can reduce the risk of unauthorized access and protect their privacy.
Data Breach
A data breach is a critical component of the "lauren kimripley leak," as it represents the security incident that led to the unauthorized access of sensitive information. Data breaches can occur due to various factors, including hacking, malware, or system vulnerabilities. In the case of the "lauren kimripley leak," a data breach allowed unauthorized individuals to gain access to a database containing personal information, including names, addresses, and financial data.
Understanding the connection between data breaches and unauthorized access to sensitive information is crucial for individuals and organizations to take proactive steps to safeguard their data. By implementing robust cybersecurity measures, such as strong passwords, firewalls, and encryption, individuals can reduce the risk of data breaches and protect their privacy.
In conclusion, data breaches are a serious threat to personal and organizational security. By understanding the connection between data breaches and unauthorized access to sensitive information, individuals and organizations can take proactive steps to protect their data and mitigate the risks associated with data breaches.
Identity Theft
The "lauren kimripley leak" underscores the serious connection between data breaches and identity theft, as the stolen personal information can be exploited for fraudulent purposes. Identity theft involves using stolen personal data, such as names, addresses, and financial information, to impersonate victims and commit crimes.
- Financial Fraud: Criminals use stolen personal information to open fraudulent accounts, make unauthorized purchases, or obtain loans in the victim's name.
- Medical Identity Theft: Stolen personal information can be used to obtain medical services or prescription drugs in the victim's name, leading to incorrect medical records and potential health risks.
- Government Benefits Fraud: Stolen personal information can be used to file fraudulent claims for government benefits, such as unemployment insurance or tax refunds.
- Criminal Impersonation: Stolen personal information can be used to create fake IDs or documents, allowing criminals to impersonate victims and commit crimes in their name.
Understanding the connection between identity theft and data breaches empowers individuals to take proactive steps to protect their personal information. By using strong passwords, being cautious about sharing personal information online, and monitoring their credit reports, individuals can reduce the risk of identity theft and safeguard their financial and personal well-being.
Reputational Damage
The "lauren kimripley leak" exemplifies the severe connection between data breaches and reputational damage. When sensitive personal information is leaked, it can have a devastating impact on an individual's reputation, both personally and professionally.
Leaked information can include embarrassing or incriminating details, which can be used to damage an individual's character or credibility. This can lead to public ridicule, loss of trust, and damage to professional relationships.
In the case of the "lauren kimripley leak," the leaked information included personal communications and financial records. This information was used to spread rumors and false accusations, damaging Lauren Kimripley's reputation and causing her significant distress.
Understanding the connection between data breaches and reputational damage is crucial for individuals and organizations to take proactive steps to protect their personal information. By implementing robust cybersecurity measures, using strong passwords, and being cautious about sharing personal information online, individuals can reduce the risk of data breaches and safeguard their reputation.
Financial Loss
The "lauren kimripley leak" underscores the severe connection between data breaches and financial loss. When sensitive financial data is leaked, it can lead to significant monetary damages for the affected individuals.
In the case of the "lauren kimripley leak," the leaked financial information included bank account numbers, credit card details, and investment records. This information was used by criminals to make unauthorized purchases, withdraw funds, and open new accounts in Lauren Kimripley's name.
Understanding the connection between data breaches and financial loss is crucial for individuals and organizations to take proactive steps to protect their financial data. By implementing robust cybersecurity measures, using strong passwords, and being cautious about sharing personal information online, individuals can reduce the risk of data breaches and safeguard their financial well-being.
Privacy Violation
In the context of the "lauren kimripley leak," the connection between privacy violation and the unauthorized disclosure of personal information is undeniable.
- Unauthorised Access and Disclosure:
The leak involved the unauthorized access and disclosure of Lauren Kimripley's personal information, including communications, financial records, and other sensitive data.
- Public Humiliation and Distress:
The disclosure of such personal information caused Lauren Kimripley significant public humiliation, distress, and emotional harm.
In conclusion, the "lauren kimripley leak" serves as a stark reminder of the importance of protecting personal privacy.
Legal Consequences
In the context of the "lauren kimripley leak," understanding the legal consequences for those responsible for data leaks is crucial. Legal frameworks aim to deter and punish individuals or organizations that engage in unauthorized access, disclosure, or misuse of personal information.
- Data Protection Laws:
Many jurisdictions have enacted comprehensive data protection laws that impose legal obligations on organizations to safeguard personal information. These laws often include provisions for civil and criminal penalties for data breaches and unauthorized disclosure of personal data.
- Cybercrime Laws:
In addition to data protection laws, many countries have enacted specific cybercrime laws that criminalize unauthorized access to computer systems and data. These laws can be used to prosecute individuals who engage in hacking, phishing, or other malicious activities that lead to data breaches.
- Negligence and Breach of Contract:
In some cases, organizations may be held liable for data breaches due to negligence or breach of contract. For example, if an organization fails to implement reasonable security measures to protect personal data, it may be found liable for damages caused by a data breach.
- Reputational Damage and Loss of Trust:
Data breaches can also lead to significant reputational damage and loss of trust for organizations. This can result in loss of customers, partners, and investors, as well as damage to the organization's brand and reputation.
In conclusion, the "lauren kimripley leak" highlights the importance of understanding the legal consequences associated with data breaches and unauthorized disclosure of personal information. Legal frameworks provide a means to hold individuals and organizations accountable for their actions and deter future data breaches.
Cybersecurity Measures
The "lauren kimripley leak" underscores the critical connection between cybersecurity measures and the protection of personal data. Cybersecurity measures are a comprehensive set of steps and technologies employed to safeguard data from unauthorized access, disclosure, or misuse. These measures are essential to prevent data breaches and protect the privacy and security of individuals and organizations.
In the case of the "lauren kimripley leak," inadequate cybersecurity measures allowed unauthorized individuals to gain access to a database containing personal information, including names, addresses, and financial data. This data breach highlights the importance of implementing robust cybersecurity measures to deter and prevent unauthorized access to sensitive information.
Organizations and individuals must prioritize cybersecurity measures to protect against data breaches and unauthorized access to personal data. Implementing strong passwords, using encryption technologies, and educating employees about cybersecurity best practices are crucial steps in safeguarding data. By understanding the connection between cybersecurity measures and data breaches, we can take proactive steps to protect our personal information and prevent future incidents like the "lauren kimripley leak."
Frequently Asked Questions on the "lauren kimripley leak"
The "lauren kimripley leak" has raised several concerns and questions. This FAQ section aims to provide concise and informative answers to some commonly asked questions.
Question 1: What is the "lauren kimripley leak"?
Answer: The "lauren kimripley leak" refers to an incident involving the unauthorized release of private information belonging to an individual named Lauren Kimripley. The leaked information included personal communications, financial records, and other sensitive data.
Question 2: How did the leak occur?
Answer: The leak occurred due to a data breach, where unauthorized individuals gained access to a database containing Lauren Kimripley's personal information. The data breach was reportedly caused by a vulnerability in the software system used by the organization storing the data.
Question 3: What are the potential consequences of the leak?
Answer: The leak can have severe consequences for Lauren Kimripley, including identity theft, financial loss, reputational damage, and emotional distress. It can also damage the trust between individuals and organizations responsible for safeguarding personal information.
Question 4: What measures can be taken to prevent similar leaks in the future?
Answer: Organizations and individuals can take several steps to prevent similar leaks, such as implementing robust cybersecurity measures, educating employees about data protection best practices, and regularly reviewing and updating security protocols.
Question 5: What legal recourse is available to victims of data leaks?
Answer: Victims of data leaks may have legal recourse depending on the jurisdiction and the specific circumstances of the leak. They may be able to file lawsuits against the responsible parties for damages, such as financial losses or emotional distress.
Question 6: What are the key takeaways from this incident?
Answer: The "lauren kimripley leak" highlights the importance of protecting personal information, implementing robust cybersecurity measures, and holding organizations accountable for safeguarding data. It also underscores the need for individuals to be vigilant about their online activities and to take steps to protect their privacy.
Remember, if you have any further questions or concerns regarding the "lauren kimripley leak" or data privacy, do not hesitate to seek guidance from legal professionals or reputable sources of information.
Transition to the next article section...
Tips to Protect Yourself from Data Leaks and Identity Theft
In light of the recent "lauren kimripley leak," it is crucial to prioritize the protection of your personal information and digital security. Here are several essential tips to help you safeguard your data and prevent identity theft:
Tip 1: Use Strong and Unique Passwords: Create complex passwords that are at least 12 characters long and include a combination of upper and lowercase letters, numbers, and symbols. Avoid using the same password for multiple accounts.
Tip 2: Enable Two-Factor Authentication: Whenever possible, activate two-factor authentication (2FA) for your online accounts. This adds an extra layer of security by requiring you to provide a second form of verification, such as a code sent to your phone, when logging in.
Tip 3: Be Cautious About Sharing Personal Information Online: Limit the amount of personal information you share on social media and other online platforms. Avoid posting sensitive data, such as your full name, address, or financial information.
Tip 4: Keep Software and Devices Updated: Regularly update your operating system, software, and apps to patch security vulnerabilities that could be exploited by hackers.
Tip 5: Use a Virtual Private Network (VPN): When using public Wi-Fi networks, consider using a VPN to encrypt your internet traffic and protect your data from eavesdropping.
Tip 6: Monitor Your Credit Reports: Regularly check your credit reports from all three major credit bureaus (Equifax, Experian, and TransUnion) for any unauthorized activity or suspicious inquiries.
Tip 7: Freeze Your Credit: If you are concerned about identity theft, consider freezing your credit with the major credit bureaus. This will prevent potential fraudsters from opening new accounts in your name.
Tip 8: Educate Yourself About Data Breaches: Stay informed about the latest data breaches and security threats. Follow reputable sources for cybersecurity news and updates.
Key Takeaways: By following these tips, you can significantly reduce the risk of becoming a victim of data leaks and identity theft. Remember, protecting your personal information is an ongoing process that requires vigilance and proactive measures.
Consider sharing these tips with friends, family, and colleagues to raise awareness about the importance of data privacy and security.
Conclusion
The "lauren kimripley leak" serves as a sobering reminder of the critical importance of data privacy and security in the digital age. This incident highlights the severe consequences that can result from unauthorized access and disclosure of personal information.
As technology continues to advance, so do the threats to our personal data. It is essential for individuals and organizations alike to take proactive measures to protect their sensitive information from falling into the wrong hands.
By implementing robust cybersecurity measures, educating ourselves about data privacy risks, and holding organizations accountable for safeguarding our data, we can create a more secure and trustworthy digital environment for all.
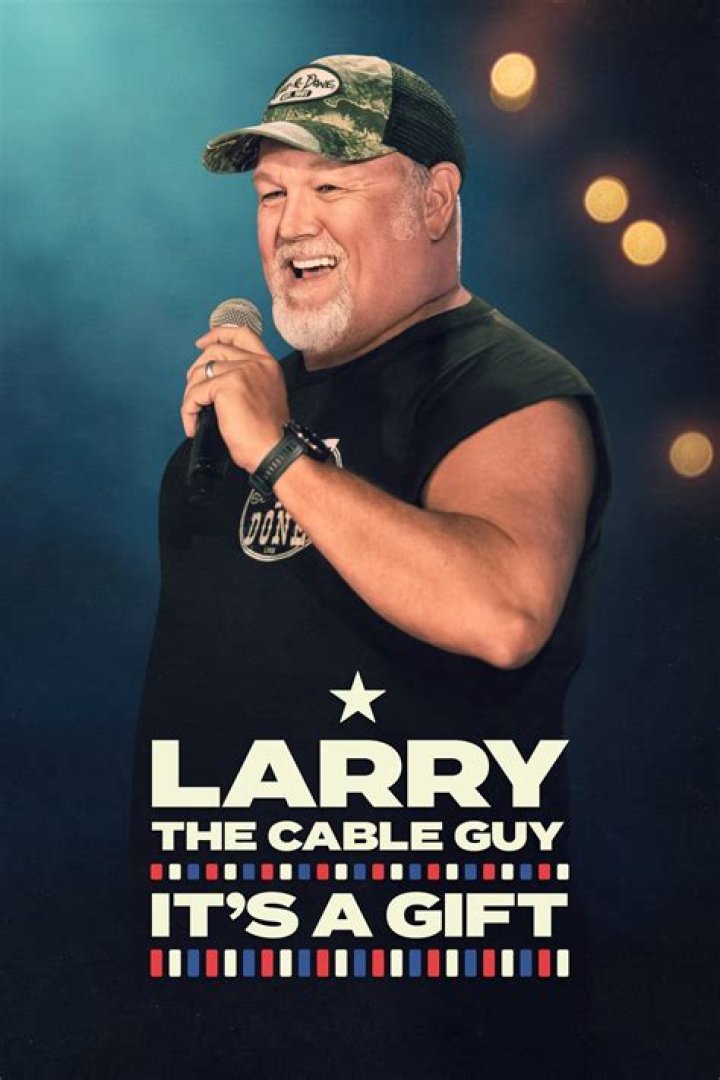
Unveiling Larry The Cable Guy's Asheville Connection: Discoveries And Insights
Unveiling The Essence Of "Li Touche M" Lyrics: Discoveries And Insights
Unveiling The Unbreakable Bond Of Celebrity Couple: Neil Arce And Maxene Magalona